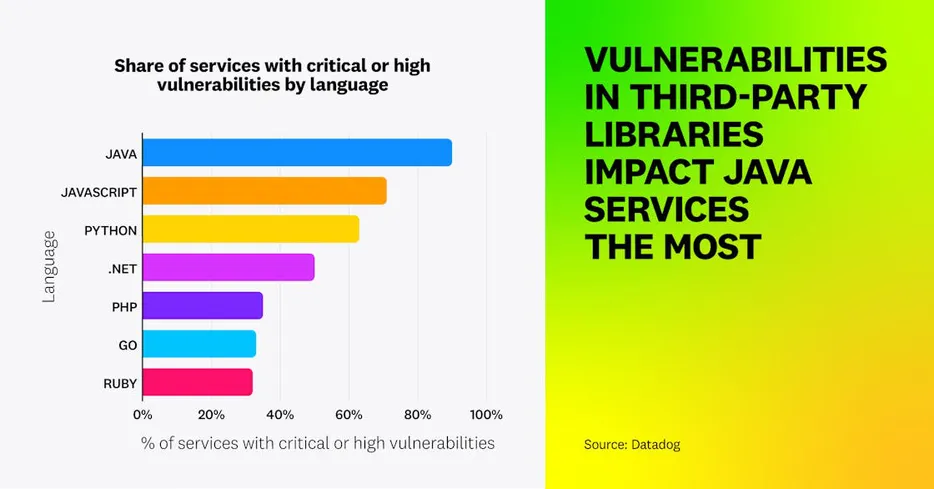
An analysis of security posture across a range of applications written in various programming languages found that Java services are disproportionately affected by vulnerabilities, with a high percentage of services vulnerable to critical, high-severity issues introduced by third-party libraries. Vulnerabilities in Java services often originate from indirect dependencies, emphasizing the importance of considering the full dependency tree and regularly updating dependencies to mitigate risks. Priority frameworks for vulnerability assessment and efficient infrastructure code practices, such as using lightweight container images and implementing Infrastructure as Code (IaC) with version control, are crucial for organizations to address cybersecurity threats effectively and reduce potential risks.
Start blogging about your favorite technologies, reach more readers and earn rewards!
Join other developers and claim your FAUN account now!











Only registered users can post comments. Please, login or signup.