As for the start, lets get to know our environment. This is my development and testing environment.
- Docker Desktop for Mac : Version 4.9.0
- Kubernetes version (Client & Server) : v1.24.0
- Helm version : v3.9.0
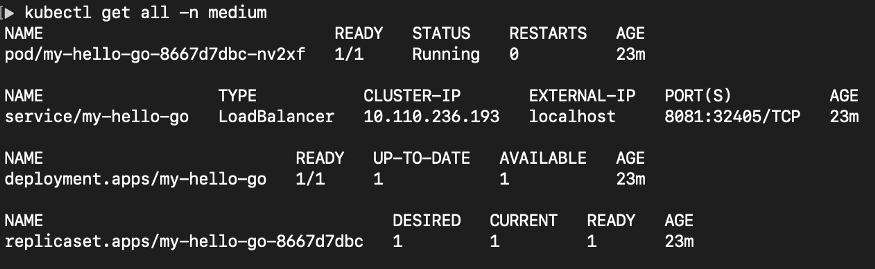
I am trying out anujarosha/hello-go chart from the Artifact HUB. Firstly I’ll add the Helm repository to my local machine using following command.