What is Kong?
Kong is an API Gateway that provides a flexible abstraction layer to securely manage communication between clients and microservices through an API.
Kong is a Lua application running on top of nginx. The flexibility of such solution allows for extend functionality by creating custom plugins (native in Lua or GO, JS etc.) that can interact with the request/response flow, communicate with the upstream, or log processes.
Once Kong is running, every request will reach Kong first, and then it will be proxied to the destination service. Between the request and the response, Kong will execute any plugin that you decide to install. Kong effectively becomes the entry point for all API requests.
Kong Plugins
Kong as an API gateway operates in layer 7 (HTTP) which makes it a universal solution that can operate flexible on many levels. One of them is presented in the Workshop section.
Official plugins are hosted on https://docs.konghq.com/hub/. Their source code is located in the “kong” repository https://github.com/Kong/kong/tree/master/kong/plugins, which can be used as a starting point for creating your own plugins. Plugins are also bundled in any deployed Kong. For more information, see https://docs.konghq.com/gateway/2.8.x/plugin-development/file-structure/. Kong documentation is well maintaned, so it is more convenient to refer to it rather than copy here.
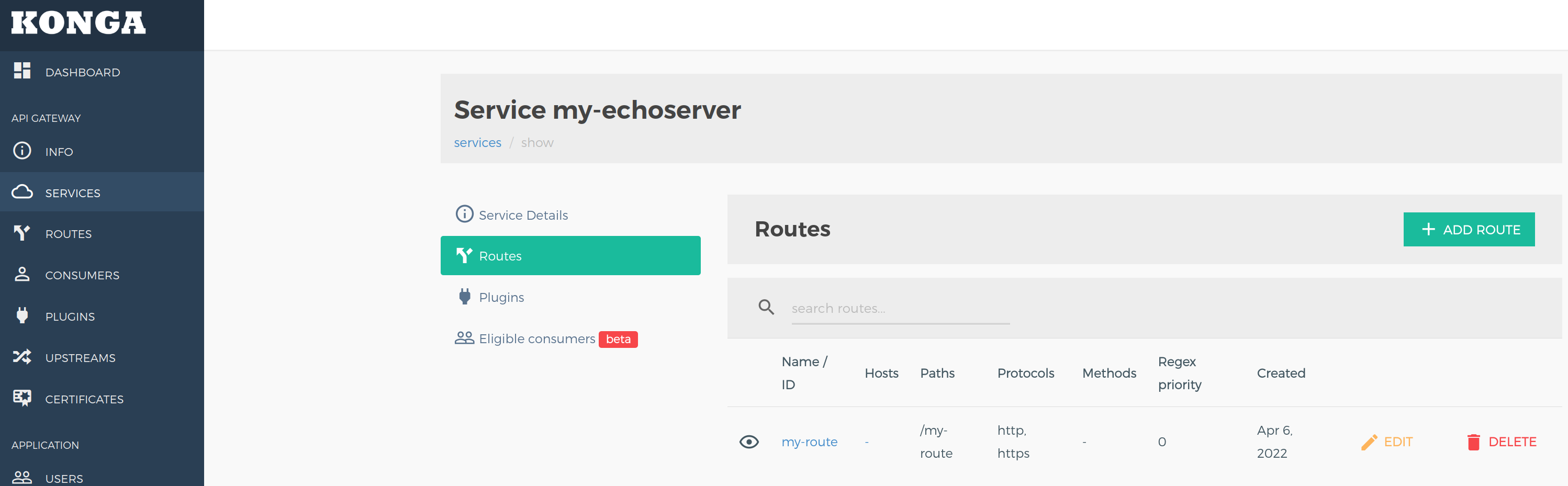
If you want to develop your own plugins, you need to create a proper environment where you can craft them. My choice was docker-compose, which has all Kong related must-have components, such as Kong and Postgres as a datastore. In my stack, I included Konga which is a GUI for Kong. Plugins use mount binding to a Kong container so after a plugin changes, you must execute the docker restart my-kong command.
Workshop
Objective
- I want to receive a response from “my-echoserver”, which is a container without Docker port mapping so ports are not available on localhost
- I want to inspect JWT tokens and:
- Refuse expired tokens
- Get specific claim from a token and add it to the response header
- I want to create an Admin API endpoint that will return a static text string