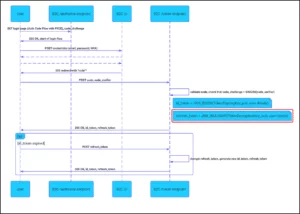
The Azure B2C service from Microsoft had a cryptographic flaw that allowed an attacker to create an OAuth refresh token with the contents for any user account. This vulnerability was reported to Microsoft by Praetorian in March 2021 and July 2022. Microsoft applied two changes in December 2022 and February 2023, but previously exploited Azure B2C environments may still be vulnerable until the rollout of Microsoft’s second fix is complete on Feb 15, 2023.
The vulnerability can potentially compromise any account in a B2C environment from an unauthenticated attacker using only account identifiers. Azure B2C environments with custom policies, configured applications with the OAuth Authorization code flow (with PKCE), and configurations as described in Microsoft’s tutorial documentation are likely to be susceptible to the vulnerability.
The business impact could vary depending on the design of an application associated with other Azure B2C environments. Praetorian recommends that Azure B2C customers perform their own risk assessment and consider remediation guidance, which includes key rotation or changing to a secret key type for AES encryption.
Microsoft resolved the information disclosure portion of this vulnerability in a way that does not require an update or configuration change by end users. Microsoft addressed the “crypto misuse” of this vulnerability by adding a new element to the refresh token contents signed with a key owned and controlled by Microsoft.
Praetorian recommends that security teams consider undertaking blue team or incident response activities, depending on the business risk, if an Azure B2C application is of particularly high-value to an organization. Praetorian also recommends that Microsoft use a nested JWT for a robust solution for JWTs.
Give a Pawfive to this post!
Start writing about what excites you in tech — connect with developers, grow your voice, and get rewarded.
Join other developers and claim your FAUN.dev() account now!















