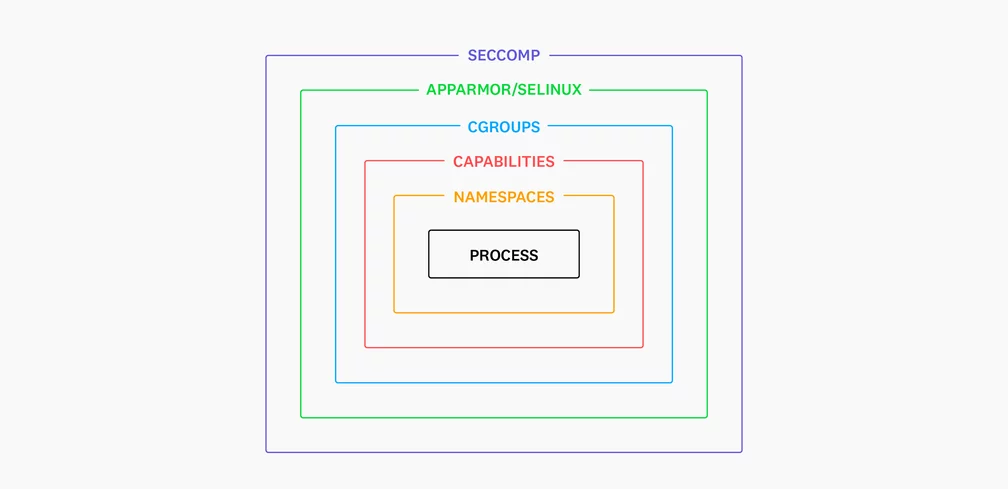
This post is about the use of Linux namespaces as the primary mechanism for providing container isolation.
The post covers the different types of namespaces and how they are used to isolate a container's process view from that of the host system.
Linux namespace allows for fine-grained isolation between different containers, and the post provides information on how to troubleshoot container security issues using standard Linux tooling.
The post also touches on control groups, which are used to manage resource usage, and user namespaces to help improve container security by creating a separate user namespace for container processes.
Give a Pawfive to this post!
Start writing about what excites you in tech — connect with developers, grow your voice, and get rewarded.
Join other developers and claim your FAUN.dev() account now!















