This two-part blog series explores how the security of Visual Studio Code (VSCode) extensions can lead to the compromise of a user’s local machine, demonstrating vulnerabilities in Microsoft’s SARIF viewer and Live Preview extensions.
The author discovered a high-severity bug in both extensions that would allow an attacker to steal all of a user’s local files. One of the bugs even allowed attackers to steal SSH keys if a user visited a malicious website while the extension was running in the background.
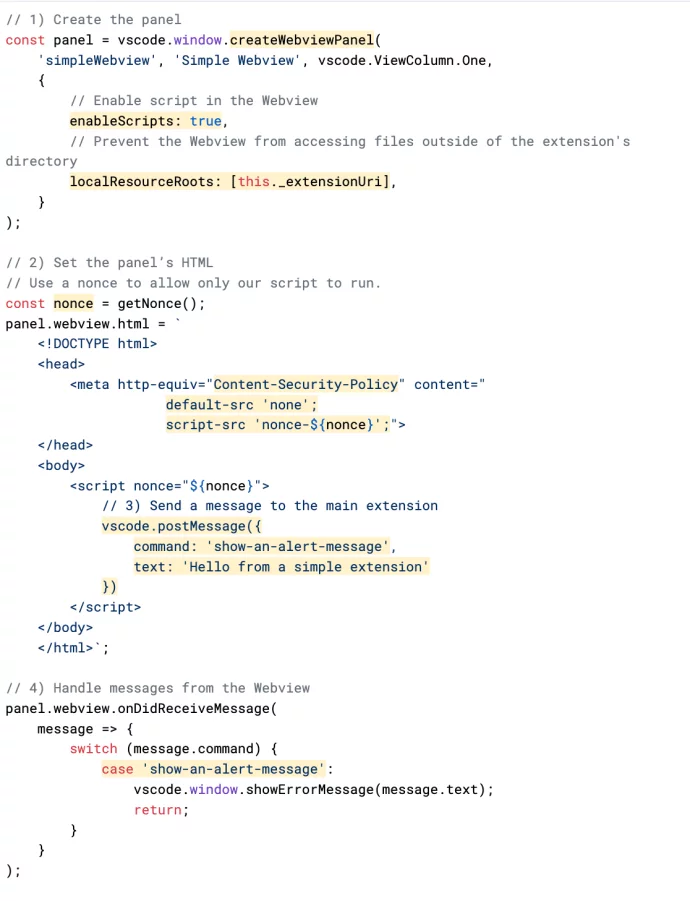
Additionally, the author explores the use of VSCode Webviews and analyses three vulnerabilities in VSCode extensions, demonstrating how an attacker can use them to exfiltrate files, execute JavaScript, and elevate the impact of their exploits using DNS rebinding.
Give a Pawfive to this post!
Start writing about what excites you in tech — connect with developers, grow your voice, and get rewarded.
Join other developers and claim your FAUN.dev() account now!















