Supply Chain Attack on Axios Pulls Malicious Dependency from npm
A supply chain attack on Axios introduced a malicious dependency, plain-crypto-js@4.2.1, published minutes earlier and absent from the project’s GitHub releases... read more
A supply chain attack on Axios introduced a malicious dependency, plain-crypto-js@4.2.1, published minutes earlier and absent from the project’s GitHub releases... read more
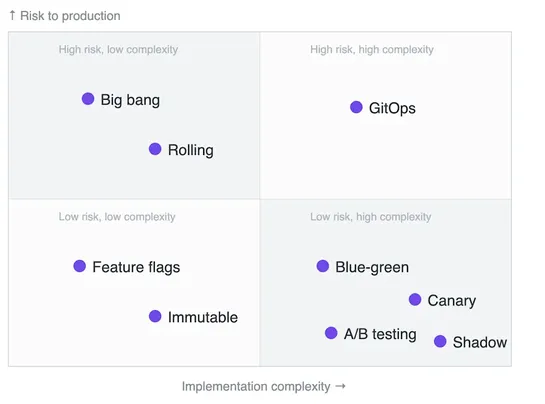
Deployment strategies control traffic shifts, rollback speed, and release risk. Options:canary,blue‑green,rolling,feature flags,shadow,immutable, andGitOps. Strategies trade production risk for setup cost. They pair withArgo Rollouts,Kayenta,ArgoCD/Flux, service meshes, and flag platforms. Pipelines.. read more
The Register contrastszramandzswap. It flags a patch that claims up to 50% fasterzramops. It notes Fedora enableszramby default. It details thatzramprovides compressed in‑RAM swap (LZ4).zswapcompresses pages before writing to disk and requires on‑disk swap... read more
The post discusses performance issues related to page counts, long cron-job reads, RAM pressure, and offloading work to background jobs. It also touches on common sources of front-end performance issues, the importance of running EXPLAIN on DB queries, and the benefits of cultivating a culture of op.. read more
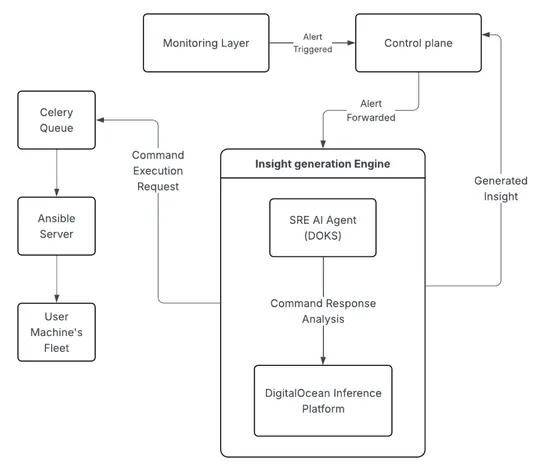
Cloudways scaled from a bootstrapped startup to a leading managed PHP hosting service, encountering challenges with growing support load. Early on, Cloudways recognized the opportunity to implement an AI-based SRE agent to reduce the burden on support teams and provide faster diagnosis and resolutio.. read more
🚀 𝘗𝘰𝘴𝘵-𝘘𝘶𝘢𝘯𝘵𝘶𝘮 𝘊𝘳𝘺𝘱𝘵𝘰𝘨𝘳𝘢𝘱𝘩𝘺: Preparing for 𝘁𝗵𝗲 𝗡𝗲𝘅𝘁 𝗖𝘆𝗯𝗲𝗿𝘀𝗲𝗰𝘂𝗿𝗶𝘁𝘆 𝗘𝗿𝗮 Quantum computers are approaching, and with them comes a threat to traditional encryption like RSA and ECC. At 𝗥𝗘𝗟𝗜𝗔𝗡𝗢𝗜𝗗, we’re taking action now to ensure your infrastructure stays secure in a post-quantum world. How we’re prepar..