Post-Quantum Cryptography in Kubernetes
Kubernetes v1.33quietly rides thepost-quantum securitywave, thanks to Go 1.24's hybrid key exchanges. Watch out for version mismatches, though—those could sneakily downgrade your defenses... read more
Kubernetes v1.33quietly rides thepost-quantum securitywave, thanks to Go 1.24's hybrid key exchanges. Watch out for version mismatches, though—those could sneakily downgrade your defenses... read more
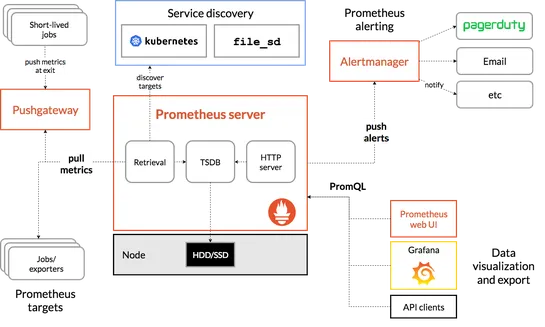
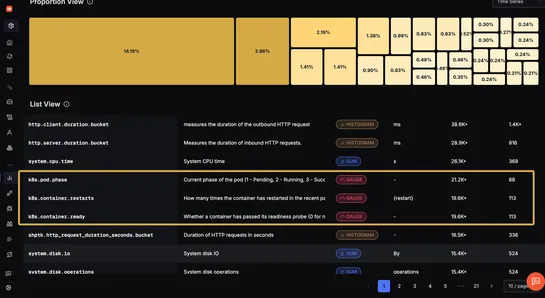
Devtronis Kubernetes monitoring on overdrive. It ropes inPrometheusandGrafana, automates the pesky setup, and shoots real-time insights straight into a slick UI. Effort? Minimal. Results? Maximal... read more
Zendeskhas tossed out the old playbook with itsFoundation Interface. Forget the guessing games of infrastructure provisioning; engineers now scribble their demands in YAML, and voilà—magic happens. Kubernetes operators step in, spinning these requests into Custom Resources. It’s self-service nirvana.. read more

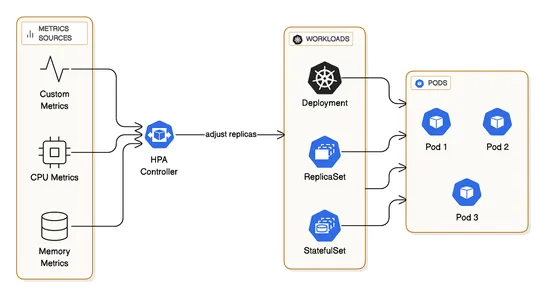
Horizontal Pod Autoscaler(HPA) cranks up pods based on CPU, memory, or custom quirks. A dream for stateless adventures, but you'll need a metrics server.Vertical Pod Autoscaler(VPA) fine-tunes CPU and memory for pods. Works like a charm for jobs where scaling out is sketchy, though it demands restar.. read more
Bitnamiclears out the virtual cobwebs by tucking its oldDebian-based imagesinto a digital time capsule, also known as theLegacy repository. It throws a friendly nudge to devs: get with the times and swap to the "latest" images. In production-ville, serious users should hitch a ride on theBitnami Sec.. read more
Kubernetes 1.33rolls out with a security upgrade. It flips the switch onuser namespacesby default, shoving pods into the safety zone as unprivileged users. Potential breaches? Curbed. But don't get too comfy—idmap-capable file systems and up-to-date runtimes are now your new best friends if you want.. read more
Red Hat OpenShift and NIC bonding for high availability is getting popular in data centers. Consider layer2/layer2+3 configurations for balanced traffic distribution across bonded links. Layer3+4 hashing offers highest throughput but may lead to out-of-order packets due to 802.3ad non-compliance. It.. read more
Kubernetes security tools usually drop the ball. Enter the dynamic duo:Tetragonwielding eBPF magic for deep observability, and smart notifications for sniper-precise alerts.Fluent Bitpairs withAzure Logic Appsin an automated setup so you can hunt down threats in real-time. Not a drop of sweat needed.. read more

OpenTelemetrydelivers a full observability package for Kubernetes—traces, metrics, logs—all without handcuffs to a single vendor. Deployyour own OTEL Collectorson Minikube usingHelm charts. Dive into node and pod-level metrics and grab those can't-miss Kubernetes cluster events... read more
Cozystackwants local cloud providers to flex by deliveringKubernetes-based managed serviceswithout breaking a sweat. Who needs hyperscalers anyway? Built on open-source goodness, it ditches vendor lock-in, giving these providers the freedom to roll out next-gen infrastructures in style... read more