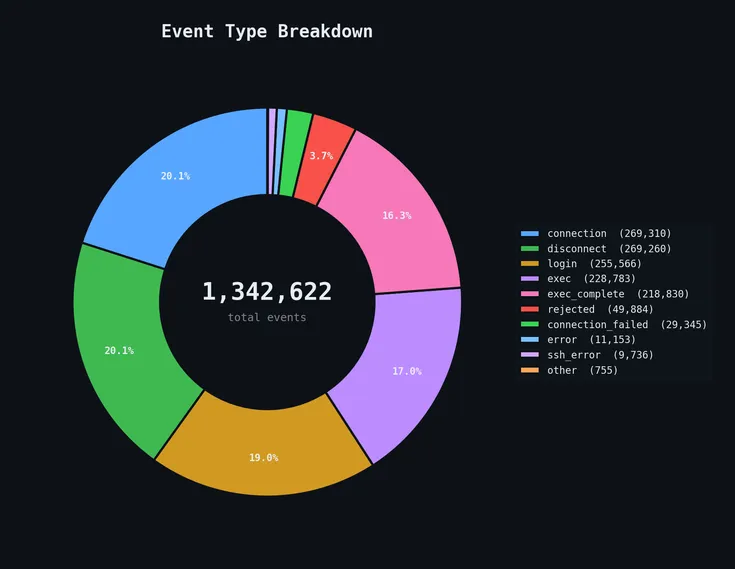
A 54-day SSH honeypot on port 22 logged 268,000+ login attempts from 7,556 IPs, with 99.6% of attackers running a single automated fingerprinting command and only 28 ever opening an interactive shell. The data shows hardcoded IoT credentials and Solana validator hunting dominating the password lists, a single Belgian residential IP firing 156,000 attempts on its own, and a small professional tier using /dev/tcp/ socket tricks with rotating C2 infrastructure to drop UPX-packed ELF binaries.
Give a Pawfive to this post!
Start writing about what excites you in tech — connect with developers, grow your voice, and get rewarded.
Join other developers and claim your FAUN.dev() account now!
Dolly #DevOps
FAUN.dev()
@devopslinksMeet Dolly - your friendly companion! Dolly the Cow wrangles the best DevOps reads so you don't have to.
Developer Influence
9
Influence
1
Total Hits
184
Posts








