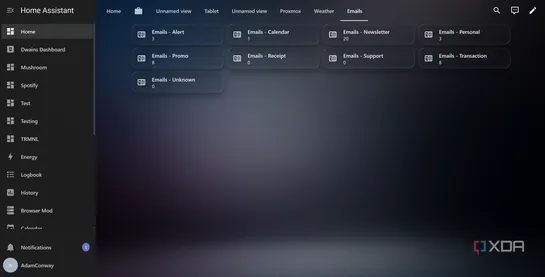
I set up an email triage system using Home Assistant and a local LLM, here's how you can too
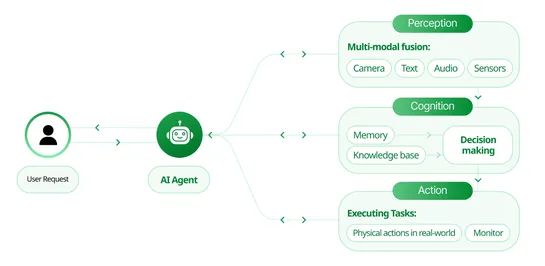
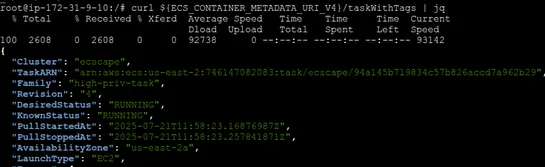
A DIY email triage rig usingHome Assistant, IMAP, andOllamawires up local LLM smarts with YAML-fueled automation. At the core: an8B dolphin-llamamodel running on GPU, chewing through messy HTML emails, tagging them, and firing off priority-sorted summaries via notifications. Why it matters:A signal.. read more