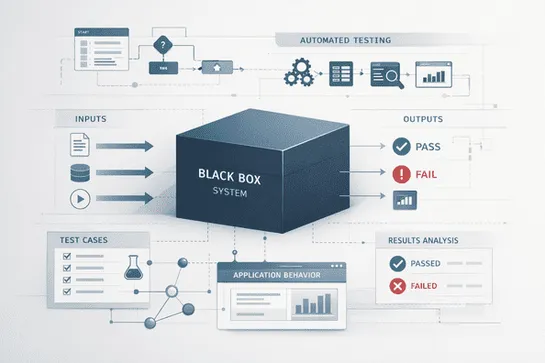
Black Box Testing Techniques to Improve Test Coverage
Learn black box testing techniques to improve test coverage. Explore methods like equivalence partitioning, boundary value analysis, and more with practical examples.
Join us
Learn black box testing techniques to improve test coverage. Explore methods like equivalence partitioning, boundary value analysis, and more with practical examples.
Hey, sign up or sign in to add a reaction to my post.
🚀 𝗪𝗼𝗿𝗹𝗱 𝗤𝘂𝗮𝗻𝘁𝘂𝗺 𝗗𝗮𝘆 𝗶𝘀 𝗵𝗲𝗿𝗲… and it’s not just science fiction anymore. Quantum computing is rapidly moving from theory to reality—and with it comes a 𝗺𝗮𝘀𝘀𝗶𝘃𝗲 𝘀𝗵𝗶𝗳𝘁 𝗶𝗻 𝗰𝘆𝗯𝗲𝗿𝘀𝗲𝗰𝘂𝗿𝗶𝘁𝘆 that organizations simply can’t ignore. Here’s the uncomfortable truth: 👉 The same technology that promises breakthrou..

Hey, sign up or sign in to add a reaction to my post.
Karpathy said we should build LLM knowledge bases. 48 hours later made Graphify was made: one command, full semantic knowledge graph.
We applied the idea to incident data turning them into a queryable and interactable semantic graph. This lets us see past fixes, predict failures, cluster services, cut alert noise, and reveal team load in seconds.
If you’re using Rootly, here is a small plugin to explore your incident data.
Check it out: github.com/Rootly-AI-Labs/rootly-graphify-importer

Hey, sign up or sign in to add a reaction to my post.
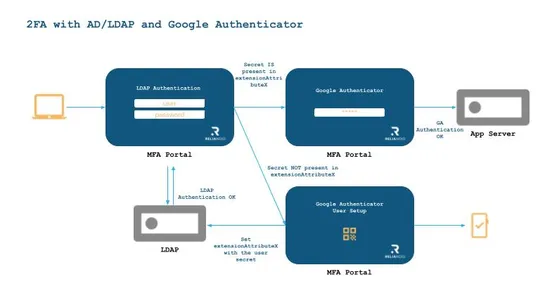
🔐 Strengthen Your MFA with Google Authenticator and RELIANOID At RELIANOID, we take authentication seriously. We've just published a new technical guide on how to integrate Google Authenticator into the RELIANOID MFA Portal, using Active Directory or LDAP to manage user secrets. ✅ Understand TOTP vs..
Hey, sign up or sign in to add a reaction to my post.
Weaknesses in product data expose themselves quickly in a multi-channel retail environment. Define a master schema, maintain control of your inventory and pricing via rules, continuously monitor for compliance, and connect performance metrics to the precise changes made for each SKU.

Hey, sign up or sign in to add a reaction to my post.
🔐 RELIANOID NIS360 Alignment & Compliance At RELIANOID, we align our security strategy with the ENISA NIS360 Cyber Risk framework—helping organizations in critical sectors strengthen resilience and improve cybersecurity maturity. From governance and risk management to incident readiness and supply..

Hey, sign up or sign in to add a reaction to my post.
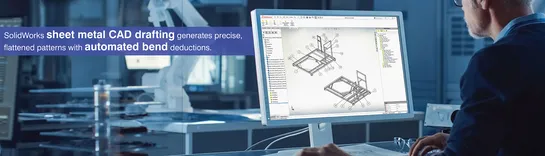
Fabricating sheet metal requires documentation that describes the designer’s intent of how to manufacture the part. By linking parametric 3D models directly to manufacturing documentation viasheet metal CAD draftingin SolidWorks, each dimension, bend note, and flat pattern is the same as what has be..
Hey, sign up or sign in to add a reaction to my post.
Kubernetes v1.36 will be released in 2 weeks. What will change? Here are prominent newly introduced alpha features in the v1.36 release: - Workload-aware preemption. Groups of related Pods are now treated as a single entity. - Topology-aware workload scheduling, allowing you to place a group of Pods..

Hey, sign up or sign in to add a reaction to my post.
🔐 𝗡𝗲𝘁𝘄𝗼𝗿𝗸 𝗔𝘁𝘁𝗮𝗰𝗸𝘀 𝟭𝟬𝟭: 𝗪𝗵𝘆 𝗕𝗼𝘁𝗻𝗲𝘁𝘀 𝗔𝗿𝗲 𝗮 𝗠𝗮𝗷𝗼𝗿 𝗧𝗵𝗿𝗲𝗮𝘁 Cyberattacks are evolving fast. Among the most common: MITM DDoS IP & DNS Spoofing Rootkits Botnets ⚠️ 𝗕𝗼𝘁𝗻𝗲𝘁𝘀 𝘀𝘁𝗮𝗻𝗱 𝗼𝘂𝘁—networks of infected devices used for DDoS, data theft, and large-scale attacks. 🛡️ 𝗛𝗼𝘄 𝗥𝗘𝗟𝗜𝗔𝗡𝗢𝗜𝗗 𝗣𝗿𝗼𝘁𝗲𝗰𝘁𝘀 𝗬𝗼𝘂 Traffic filter..
Hey, sign up or sign in to add a reaction to my post.
The blog introduces 7 reusable tooltip components built with shadcn/ui for React apps - focused on accessibility, customization, and real-world UI use cases.

Hey, sign up or sign in to add a reaction to my post.
This organization doesn't have a detailed description yet. If you are the administrator of this organization, please claim this page and edit it.
Hey there! 👋
I created FAUN.dev(), an effortless, straightforward way for busy developers to keep up with the technologies they love 🚀
