Company as Code
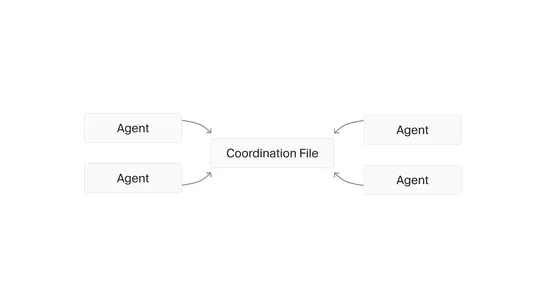
Organisations rely heavily on digital systems, yet manage important organisational data using outdated manual methods despite advanced automation capabilities in other areas. A novel "Company as Code" concept proposes a programmatic representation of the entire organisation, enabling structured, ver.. read more