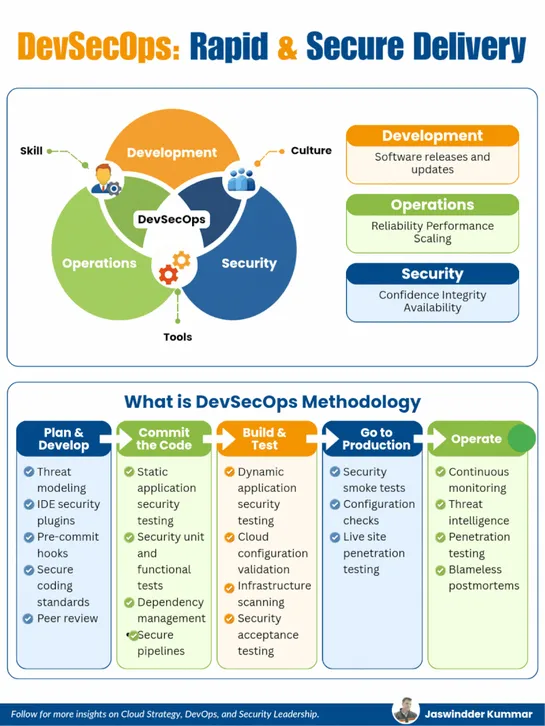
DevSecOps: Rapid & Secure Delivery
If security is your last step, you’re already too late. This guide shows how to build a DevSecOps pipeline where security is continuous, automated, and invisible to delivery speed.
Join us
If security is your last step, you’re already too late. This guide shows how to build a DevSecOps pipeline where security is continuous, automated, and invisible to delivery speed.
Hey, sign up or sign in to add a reaction to my post.
GitHub revoked Copilot's ability to inject tips into other users' pull requests after reports that Copilot Review inserted aRaycastlink. They disabled agent tips in PR comments, blamed a programming-logic bug, and said they won't turn tips into ads... read more

Hey, sign up or sign in to add a reaction to my post.
SQLite packsJSONextraction, expression indexes,FTS5full-text search,CTEs, window functions, andWALinto a single file. It enforcesstrict tables, supportsgenerated columns, and indexes JSON expressions for fast semi-structured queries... read more
Hey, sign up or sign in to add a reaction to my post.
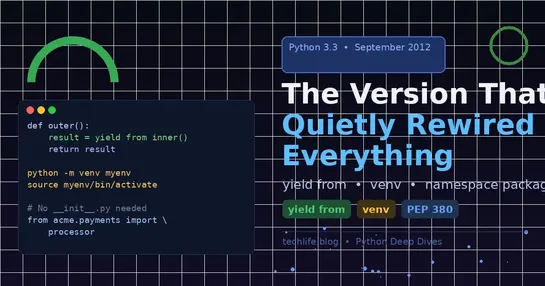
Python 3.3 introduced three key features that have had a lasting impact on Python development. Firstly, yield from simplified the composition of generators by allowing easy delegation between them. Secondly, venv standardized virtual environments in Python, improving isolation and reproducibility of.. read more
Hey, sign up or sign in to add a reaction to my post.
CTO at ZAR shares his experience managing 10 engineers, shipping code, and operating at the C-level with an AI assistant named Claude Code. The system allows him to maintain context across multiple workstreams, automate tasks, and scale his productivity. In just three weeks, he has documented 82 mee.. read more
Hey, sign up or sign in to add a reaction to my post.
The article catalogs obfuscation methods:HTML entities,SVG in an object,display:none, JavaScript decoders, custom encodings, andAES‑256. It coversmailtoobfuscation, redirects (302/301,.htaccess), interaction-gated reveals, accessibility caveats, and ahoneypot-based spam-statistics system... read more
Hey, sign up or sign in to add a reaction to my post.
GitHub hosts its own source code on github.com, creating a circular dependency. To mitigate this, GitHub maintains mirrors of its code and built assets. By using eBPF, GitHub can selectively monitor and block calls that create circular dependencies in their deployment system... read more

Hey, sign up or sign in to add a reaction to my post.
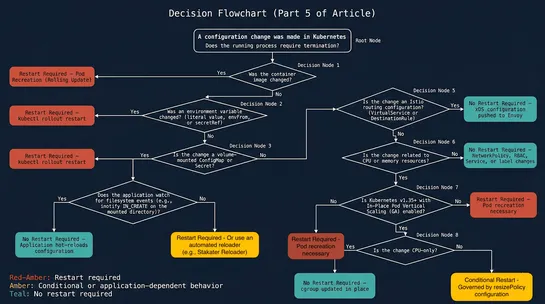
Production internals guide verified against Kubernetes 1.35 GA. Engineers need to understand terminology differences to avoid flawed runbooks and bad on-call decisions. Kubelet watches the pod spec, not other resources like ConfigMaps or Secrets, to explain the majority of config update investigatio.. read more
Hey, sign up or sign in to add a reaction to my post.
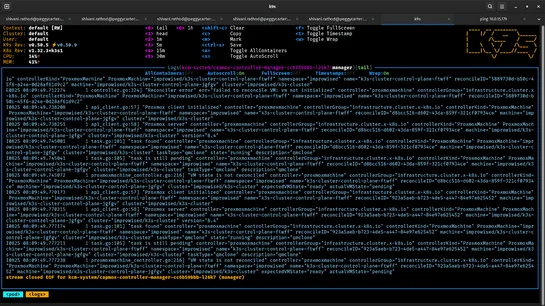
Kubernetes, now 12 years old, has evolved into the universal operating system for modern infrastructure, running on various platforms like Proxmox. Using k0rdent, Proxmox, and K3s, users can provision and manage Kubernetes clusters on-premise in a declarative, repeatable, and clean manner. This appr.. read more
Hey, sign up or sign in to add a reaction to my post.
The Kubernetes Monitoring Helm chart version 4.0 is designed to solve real pain points that users have hit as their monitoring setups have grown. Destinations are now defined as a map instead of a list, making it easier to manage configurations for multiple clusters. Collectors are defined by the us.. read more
Hey, sign up or sign in to add a reaction to my post.
Hey there! 👋
I created FAUN.dev(), an effortless, straightforward way for busy developers to keep up with the technologies they love 🚀
