OpenTelemetry Metrics in Quarkus Explained
Understand how to enable, export, and extend OpenTelemetry metrics in your Quarkus application with practical examples.
Understand how to enable, export, and extend OpenTelemetry metrics in your Quarkus application with practical examples.

Redis addresses a critical remote code execution vulnerability, CVE-2025-49844, by releasing fixed versions and recommending best practices to protect instances.

AI-powered remediation rolls out across Pulumi Cloud, bringing automated fixes, approval workflows, and cross-cloud compliance without requiring full migration to Pulumi IaC.
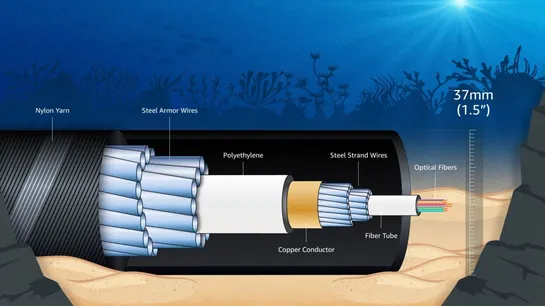
AWS introduces Fastnet, a high-capacity transatlantic subsea cable, to enhance network resilience and support growing cloud and AI demands, operational by 2028.
GitHub’s new Agent HQ unifies AI tools from OpenAI, Anthropic, and Google directly within GitHub. It offers centralized management for AI agents through mission control, custom agent setup, code quality tracking, and enterprise governance - all designed to streamline AI-driven development while keeping control and visibility in one place.

IncusOS, an immutable operating system for running Incus, debuts with atomic updates and boot security, based on a minimal Debian 13, managed via the Incus API.
🌟 We’re proud to share the latest article from our CEO, whose vision and deep technical insight continue to drive innovation at RELIANOID. In her new article — “From Single Processors to the Post-Quantum Era and Autonomous Resilience: The Next Paradigm in High Availability System Design” — she expl..
