Post-Quantum Cryptography in Kubernetes
Kubernetes v1.33quietly rides thepost-quantum securitywave, thanks to Go 1.24's hybrid key exchanges. Watch out for version mismatches, though—those could sneakily downgrade your defenses... read more
Kubernetes v1.33quietly rides thepost-quantum securitywave, thanks to Go 1.24's hybrid key exchanges. Watch out for version mismatches, though—those could sneakily downgrade your defenses... read more
Kubernetes 1.33rolls out with a security upgrade. It flips the switch onuser namespacesby default, shoving pods into the safety zone as unprivileged users. Potential breaches? Curbed. But don't get too comfy—idmap-capable file systems and up-to-date runtimes are now your new best friends if you want.. read more
Zendeskhas tossed out the old playbook with itsFoundation Interface. Forget the guessing games of infrastructure provisioning; engineers now scribble their demands in YAML, and voilà—magic happens. Kubernetes operators step in, spinning these requests into Custom Resources. It’s self-service nirvana.. read more

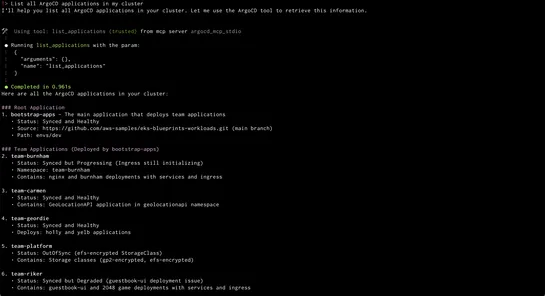
ArgoCD MCP Serverteams up withAmazon Q CLIto shake up Kubernetes with natural language controls. Finally, GitOps that even the non-tech crowd can handle. Kiss those roadblocks goodbye. No more brain strain from Kubernetes. Now, plain language syncs apps, reveals resource trees, and checks health sta.. read more
Bitnamiclears out the virtual cobwebs by tucking its oldDebian-based imagesinto a digital time capsule, also known as theLegacy repository. It throws a friendly nudge to devs: get with the times and swap to the "latest" images. In production-ville, serious users should hitch a ride on theBitnami Sec.. read more
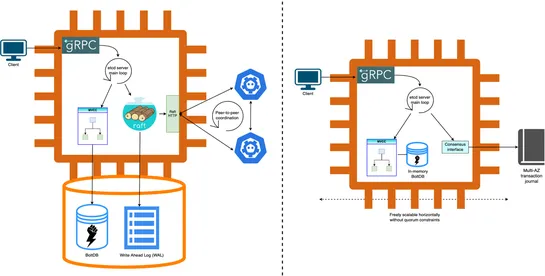
Amazon EKScranked up its gear—you can now spin up clusters with a staggering100,000 nodesat your beck and call. That’s a cozy home for either1.6 million AWS Trainium chipsor800,000 NVIDIA GPUs. Welcome to the playground for ultra-scale AI/ML. Performance soars skyward by ditching old etcd consensus .. read more
Red Hat OpenShift and NIC bonding for high availability is getting popular in data centers. Consider layer2/layer2+3 configurations for balanced traffic distribution across bonded links. Layer3+4 hashing offers highest throughput but may lead to out-of-order packets due to 802.3ad non-compliance. It.. read more
A cyberattack can strike at any time—causing operational disruption, financial loss, and reputational damage. Preparing for and effectively managing a cyber crisis is no longer optional—it's essential. At RELIANOID, we help businesses build robust cyber resilience through advanced solutions and expe..

Instrument NGINX with OpenTelemetry to capture traces, track latency, and connect upstream and downstream services in a single request flow.

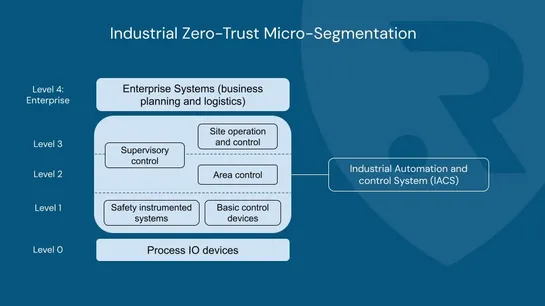
In today's connected industrial world, the convergence of IT & OT brings efficiency—but also new risks. That’s why Zero-Trust Micro-Segmentation is no longer optional. 📌 It divides your network into isolated zones, applies strict access rules, and assumes no user or device is inherently trusted. ✅ K..