Announcing Red Hat Enterprise Linux for AWS
RHEL 10for AWS makes its debut, complete with AWS-tailored performance profiles, beefed-up security, and a seamless CLI. Ready to tango with the cloud like a pro... read more
RHEL 10for AWS makes its debut, complete with AWS-tailored performance profiles, beefed-up security, and a seamless CLI. Ready to tango with the cloud like a pro... read more

A disaster recovery plan relies on a coordinated incident response team. The speed and coordination of this team are crucial for minimizing downtime and keeping the organization running smoothly during a crisis. Key roles within the incident response team include incident commander, technical lead, .. read more
KubernetesonDebianjust got its act together. The team axed the messy vendoring, shrunk the tarball bulk by over half, and tidied up dependency chaos. Now every dependency snuggles into Debian nicely, kicking out those pesky proprietary blobs. This means a secure, policy-friendly package and—drumroll.. read more
CVE-2025-47933inArgo CDshreds security and hands injected JavaScript the keys to your Kubernetes kingdom. With a terrifyingCVSS score of 9.1, this one's no joke. Patch it, yesterday!.. read more
Woodpeckertakes on the dirty work of red teaming for AI, Kubernetes, and APIs. It tackles over half of the OWASP Top 10 threats without breaking a sweat. Find it free on GitHub, spreading top-notch security testing like free candy... read more

Modular monolithsrisk turning into messy "big balls of mud" when developers overdo shortcuts or tangle the code. Gomodular-firstand be ready to spot stealthy dependencies lurking in the corners. Skip the quick fixes—they're overrated... read more

k0s, the streamlined Kubernetes flavor pioneered by theCNCF Sandbox, strips it down to one slick binary. It's tailor-made for edge AI, shedding the bulky baggage. UnlikeK3s, k0s thrives on meager resources, sipping energy while skipping the tangled installation dance. Just 1-2 GB of RAM, and you're .. read more
A wild440%spike in Kubernetes vulnerabilities over five years calls for open-source security tools that actually get the job done. Still, half of the organizations feel like they're playing catch-up trying to lock it down. Enter tools likeFalcoandIstio. Falco sniffs out runtime anomalies while Istio.. read more
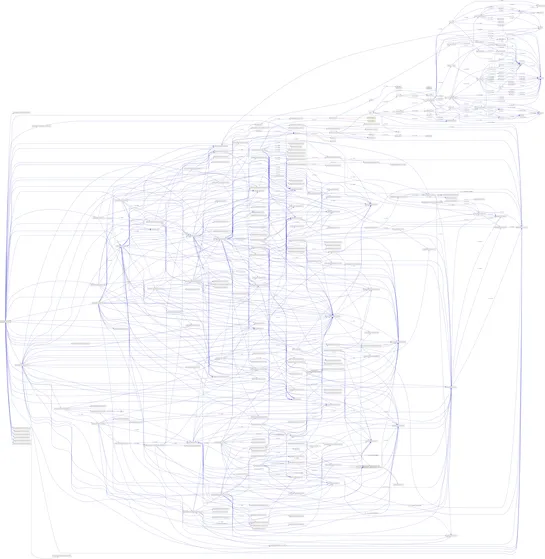
Orca Research Pod discovered two bugs in kro that could allow an attacker to introduce a malicious CustomResourceDefinition (CRD). Kro is an open-source project enabling custom Kubernetes APIs using ResourceGraphDefinition resources. These vulnerabilities could lead to a confused deputy scenario whe.. read more
Kubernetes v1.33crushes it for AI/ML workloads with slickDynamic Resource Allocation.Your GPU headaches? Gone. It's nimble, modular, and ready to scale. Plus, with topology-aware routing now in the spotlight, Kubernetes slashes network latency and trims cloud expenses by favoring the nearest options.. read more
