A new stealth rootkit called LinkPro just surfaced, taking aim at AWS-hosted Linux boxes. It blends two custom eBPF programs for deep concealment and remote activation via magic packets.
The path in? CVE-2024-23897 - an RCE on a public Jenkins server. From there, attackers slipped into Amazon EKS clusters, dropped vShell (an in-memory backdoor), and escaped containers using a poisoned Docker image.
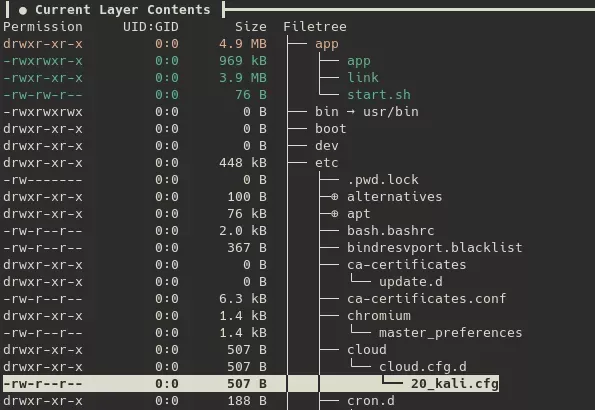
LinkPro keeps itself hidden with Tracepoint and Kretprobe hooks - masking processes, files, even its own eBPF code. If eBPF tracing isn’t available, it downgrades to an old-school trick: an LD_PRELOAD shared lib.