The article summarizes the discovery of three distinct remote code execution (RCE) vulnerabilities found in the widely played Counter-Strike: Global Offensive game.
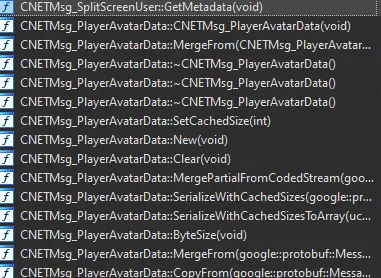
The vulnerabilities are activated when the game client establishes a connection with a malevolent python CS:GO server. The post chronicles the process of examining the CS:GO binary and dives into the technical intricacies of the identified bugs.
The article concludes by showcasing a proof of concept (POC) exploit that capitalizes on four distinct logic flaws, resulting in remote code execution on the game's client whenever it connects to the server.
Give a Pawfive to this post!
Start writing about what excites you in tech — connect with developers, grow your voice, and get rewarded.
Join other developers and claim your FAUN.dev() account now!















