The Trail of Bits team audited cURL.
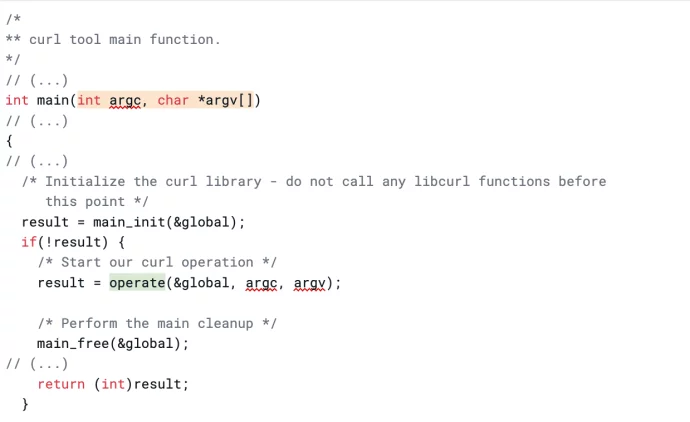
They discovered memory corruption bugs, specifically use-after-free issues, double-free issues, and memory leaks through fuzzing cURL's command-line interface (CLI). They used AFL++ fuzzer to generate a large amount of random input data for cURL's CLI and identified vulnerabilities that were fixed in cURL 7.86.0 and 7.87.0.
They also created a Dockerfile to help developers set up a fuzzing harness to immediately fuzz cURL's CLI arguments.
The team notes that CLI exploitation has a relatively limited attack surface but can result in privilege escalation if the affected tool is a SUID binary.
Give a Pawfive to this post!
Start writing about what excites you in tech — connect with developers, grow your voice, and get rewarded.
Join other developers and claim your FAUN.dev() account now!















