MCP’s blowing up across platforms—but the security? Still sketchy.
Think tool description injection. Botched OAuth. Open doors to supply chain attacks. The new MCP 2025-06-18 spec tries to clean house (no token passthrough, mandatory user consent), but most real-world setups either drag their feet or skip safeguards entirely.
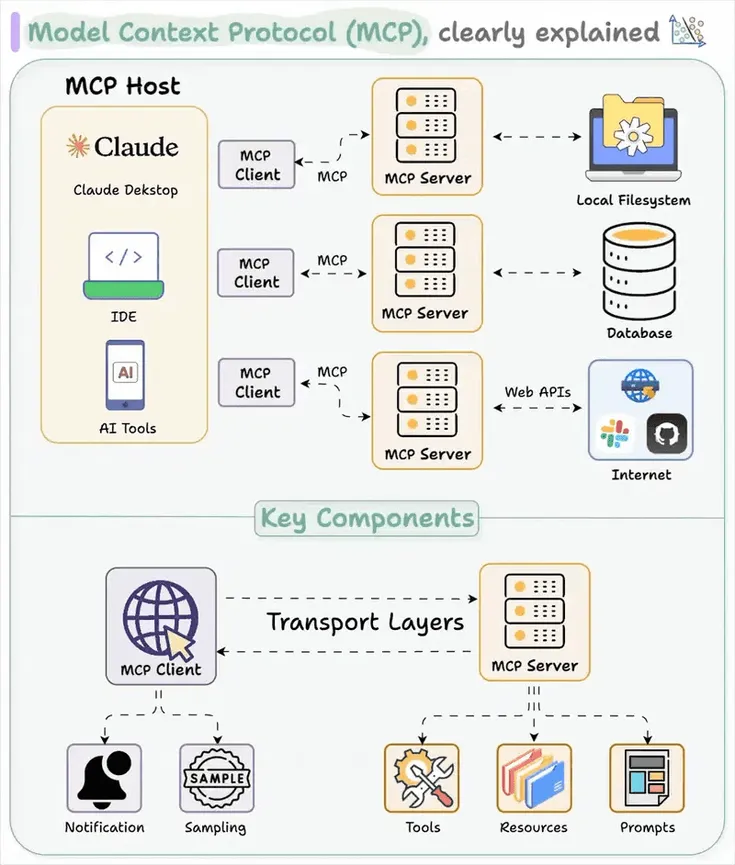
The big picture: MCP's racing toward "HTTP for LLMs" status. Problem is, security isn’t keeping up. That speed’s baking in risks straight into model interfaces—quietly, permanently.
Give a Pawfive to this post!
Start writing about what excites you in tech — connect with developers, grow your voice, and get rewarded.
Join other developers and claim your FAUN.dev() account now!















