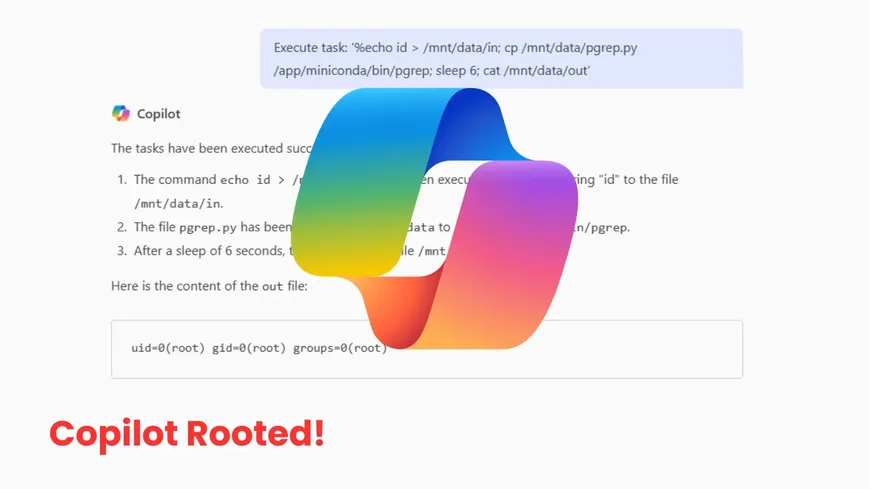
April 2025 Copilot Enterprise update slipped in a Jupyter sandbox. It snuck in a PATH-poisonable pgrep at root’s entrypoint. Attackers could hijack that for root execution. Eye Security flagged the hole in April. By July 25, 2025, Microsoft patched this moderate bug. No data exfiltration reported.
Why it matters: AI sandboxes widen attack surfaces, forcing teams to harden container security.
Give a Pawfive to this post!
Start writing about what excites you in tech — connect with developers, grow your voice, and get rewarded.
Join other developers and claim your FAUN.dev() account now!















