A simple solution to hide secrets in repository and monitoring them using Azure DevOps's build validation policy: write one script to scan the repository for secrets, create a comprehensive monitoring dashboard, suppress false positives, alert developers when trying to add secrets to the repository, and block production delivery until secrets are removed.
The script can work with Azure DevOps and GitHub.
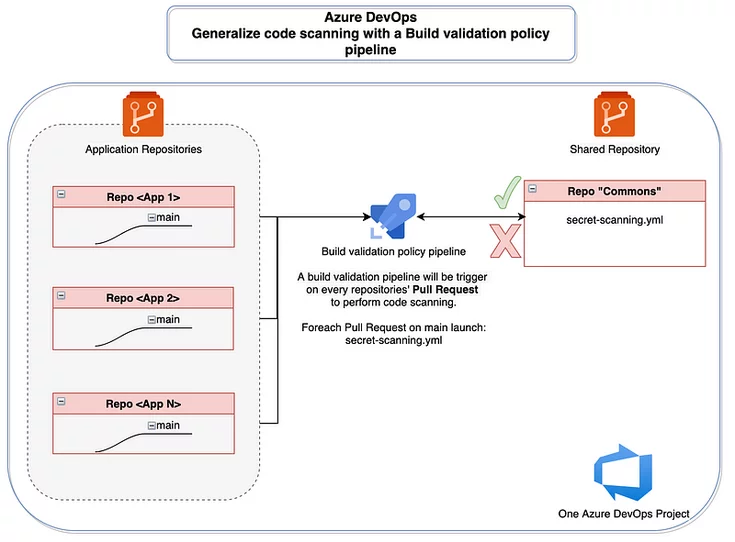
Azure DevOps features, including the security scan credscan tool and the sarif sast scan tab, can be invoked to perform security scans on the pipeline. A pipeline is created to perform security scans on every pull request made to the production branch.
The policy can be enforced through the organization workbook.
Give a Pawfive to this post!
Start writing about what excites you in tech — connect with developers, grow your voice, and get rewarded.
Join other developers and claim your FAUN.dev() account now!















