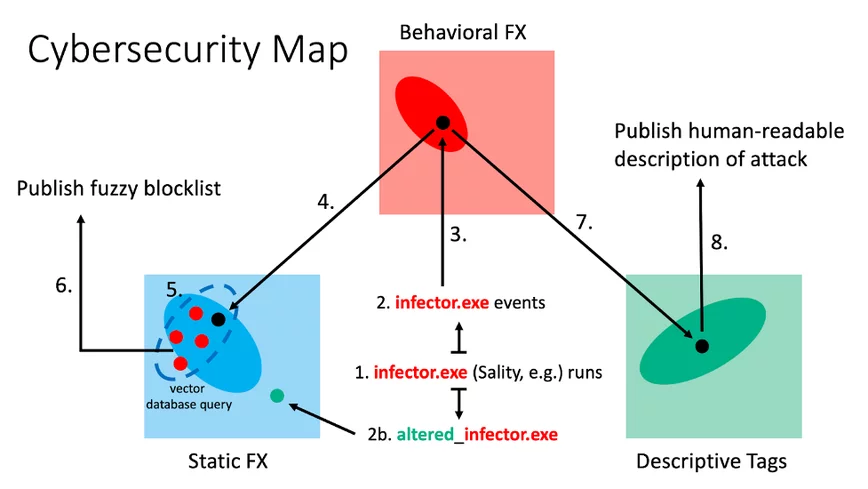
CrowdStrike data scientists have developed a new similarity paradigm that allows for the organization and accessibility of cybersecurity data. This paradigm enables scientists and analysts to effectively prevent and respond to breaches by associating different representations of important cybersecurity objects.
Give a Pawfive to this post!
Start writing about what excites you in tech — connect with developers, grow your voice, and get rewarded.
Join other developers and claim your FAUN.dev() account now!















