The Hidden AWS Cost Traps No One Warns You About (and How I Avoid Them)
Calling outfive sneaky AWS cost traps—the kind that creep in through overlooked defaults and quiet misconfigs, then blow up your bill while no one's watching... read more
Join us
Calling outfive sneaky AWS cost traps—the kind that creep in through overlooked defaults and quiet misconfigs, then blow up your bill while no one's watching... read more

Hey, sign up or sign in to add a reaction to my post.
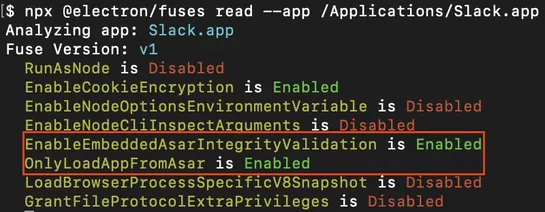
A fresh CVE (2025-55305) just put Electron apps in the hot seat. The bug? Chromium-based apps fail to treatV8 heap snapshot filesas potential attack vectors. That crack lets unsigned JavaScript slip past code signing and run inside heavyweight targets like Slack, 1Password, and Signal. The heart of.. read more
Hey, sign up or sign in to add a reaction to my post.
Lucidity has upgraded itsAutoScaler. It now handles persistent volumes on AWS-hosted Kubernetes, automatically scaling storage and reducing waste. The upgrade bringspod-level isolation,fault tolerance, andbulk Linux onboarding. Azure and GCP are next on the list... read more

Hey, sign up or sign in to add a reaction to my post.
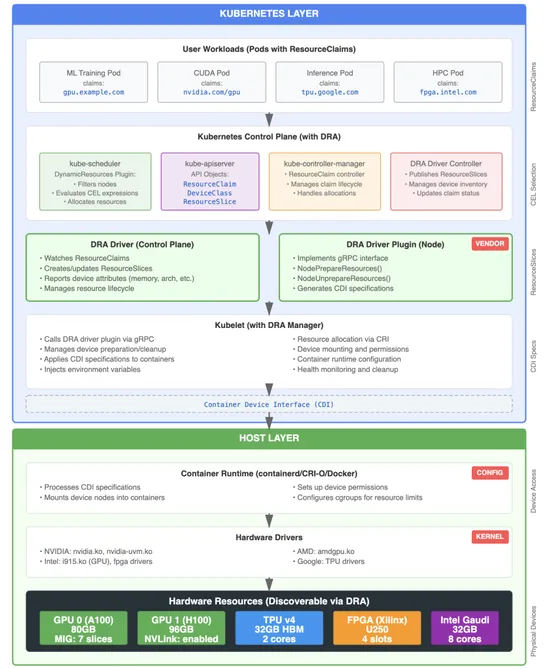
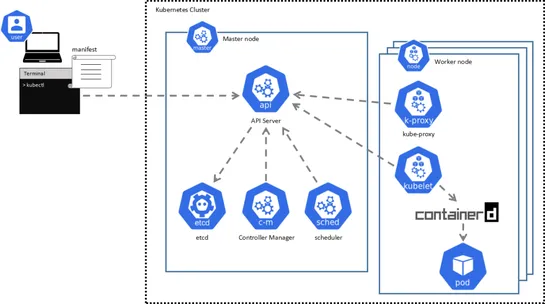
Kubernetes 1.34 brings serious heat for anyone juggling GPUs or accelerators. MeetDynamic Resource Allocation (DRA)—a new way to schedule hardware like you mean it. DRA addsResourceClaims,DeviceClasses, andResourceSlices, slicing device management away from pod specs. It replaces the old device plu.. read more
Hey, sign up or sign in to add a reaction to my post.
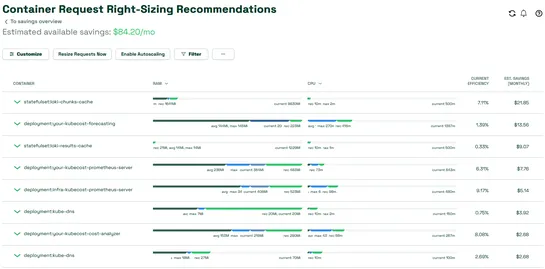
Kubecost’s Amazon EKS add-on now handlesautomated container request right-sizing. That means teams can tweak CPU and memory requests based on actual usage—once or on a recurring schedule. Optimization profiles are customizable, and resizing can be baked into cluster setup using Helm. Yes, that mean.. read more
Hey, sign up or sign in to add a reaction to my post.
Nigel Douglas discusses the challenges of security in Kubernetes, particularly with traditional base operating systems. Talos Linux offers a different approach with a secure-by-default, API-driven model specifically for Kubernetes. CISOs play a critical role in guiding organizations through the shif.. read more
Hey, sign up or sign in to add a reaction to my post.
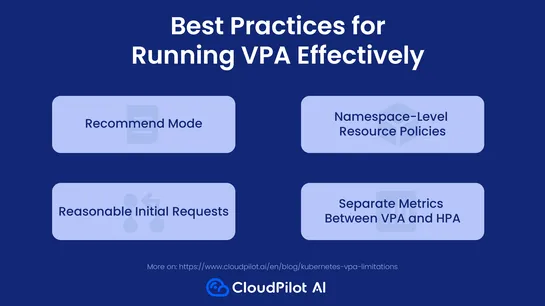
Kubernetes'Vertical Pod Autoscaler (VPA)tries to be helpful by tweaking CPU and memory requests on the fly. Problem is, it needs to bounce your pods to do it. And if you're also runningHorizontal Pod Autoscaler (HPA)on the same metrics? Now they're fighting over control. VPA sees a narrow slice of .. read more
Hey, sign up or sign in to add a reaction to my post.
A new attack chain messes withKubernetes DNS resolutionandArgoCD’s certificate injectionto swipe GitHub credentials. With the right permissions, a user inside the cluster can reroute GitOps traffic to a fake internal service, sniff auth headers, and quietly walk off with tokens. What’s broken:GitOp.. read more
Hey, sign up or sign in to add a reaction to my post.
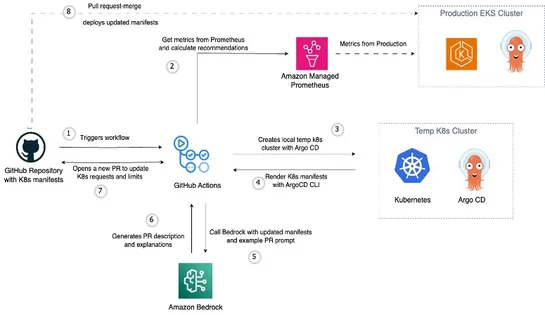
AWS just dropped a GitOps-native pattern for tuning EKS resources—built to runoutsidethe cluster. It’s wired up withAmazon Managed Service for Prometheus,Argo CD, andBedrockto automate resource recommendations straight into Git. Here’s the play: it maps usage metrics to templated manifests, then sp.. read more
Hey, sign up or sign in to add a reaction to my post.
Older container technologies like Docker have been prone to security vulnerabilities, such as CVE-2019-5736 and CVE-2022-0847, which allowed for potential host system compromise. Podman changes the game by eliminating the need for a persistent background service like the Docker daemon, enhancing sec.. read more
Hey, sign up or sign in to add a reaction to my post.
This tool doesn't have a detailed description yet. If you are the administrator of this tool, please claim this page and edit it.
Hey there! 👋
I created FAUN.dev(), an effortless, straightforward way for busy developers to keep up with the technologies they love 🚀
