ConfigHub: Why Your Internal Developer Platform Needs It
See why GitOps often feels like a sprawl of configs, discover how to manage Configuration as Data for your Kubernetes platform, and learn how ConfigHub can help... read more
Join us
See why GitOps often feels like a sprawl of configs, discover how to manage Configuration as Data for your Kubernetes platform, and learn how ConfigHub can help... read more
Hey, sign up or sign in to add a reaction to my post.
Amazon EKS just went full Fort Knox. It now runs on azero operator accessmodel - meaning even AWS can’t peek inside your Kubernetes control or data plane. The setup leans on theNitro System’s confidential compute,guarded APIs, andmulti-party approval pipelines. NCC Group also kicked the tires and ga.. read more
Hey, sign up or sign in to add a reaction to my post.
KServe is upgrading.The CNCF pulled it into incubation, backing it astheKubernetes-native way to serve both generative and predictive AI. Translation: it’s not a side project anymore - it’s core infra. Version 0.15 steps up with tighter integrations across the stack:vLLM,Envoy Gateway,llm-d,Knative,.. read more

Hey, sign up or sign in to add a reaction to my post.
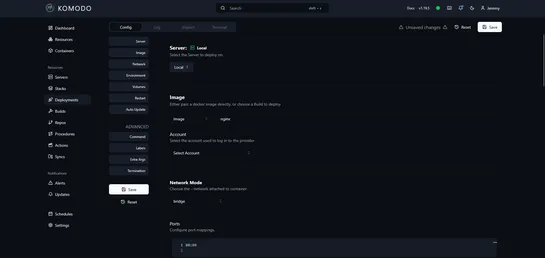
Komodo drops a slick browser-based UI for wrangling Docker - containers, images, networks, and Compose stacks - through a real-time visual dashboard. Think native Docker meets one-click redeploys, host curation via agents, and reusable container configs that don’t make you hate YAML... read more
Hey, sign up or sign in to add a reaction to my post.
NVIDIA releasedGrove, a Kubernetes API baked intoDynamo, to wrangle the chaos of modern AI inference. It pulls apart your big, messy model into clean, discrete chunks - prefill, decode, routing - and runs them like a single, orchestrated act. The trick?Custom hierarchical resources. They let Grove h.. read more
Hey, sign up or sign in to add a reaction to my post.
A tight 2-hour YouTube course built for theCKA examgrind. It's all real-world tasks: cluster setup, upgrades, troubleshooting. No fluff, just shell commands and Kubernetes in action. It walks through the gritty bits:etcdbackup and restore, node affinity, tolerations, and how to set upIngresslike som.. read more

Hey, sign up or sign in to add a reaction to my post.
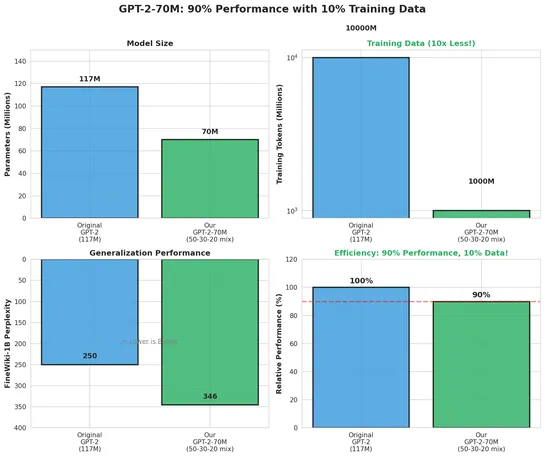
Researchers squeezed GPT-2-class performance out of a model trained on just1 billion tokens- 10× less data - by dialing in a sharp dataset mix:50% finePDFs, 30% DCLM-baseline, 20% FineWeb-Edu. Static mixing beat curriculum strategies. No catastrophic forgetting. No overfitting. And it hit90%+of GPT-.. read more
Hey, sign up or sign in to add a reaction to my post.
Nvidia CEO Jensen Huang, in some leaked comments, didn’t mince words: U.S. export bans aren’t hobbling China’s AI game - they’re fueling it. He pointed to Huawei’s 910C chip edging close to H100 territory, a forecast putting China ahead in AI compute by 2027, and a fast-growing local chip industry n.. read more

Hey, sign up or sign in to add a reaction to my post.
Amp stretches the context window into something more useful. It pulls in system prompts, tool info, runtime metadata, even AGENTS.md files - fuel for agentic behavior. It gives devs serious control: edit messages, fork threads, drop in files with @mentions, hand off conversations, or link threads to.. read more
Hey, sign up or sign in to add a reaction to my post.
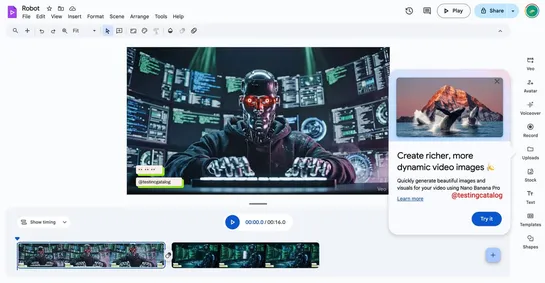
Google dropsGemini 3and the newNano Banana Pronext week. Big swing at image generation - now tied tight to Gemini 3 Pro. Early glimpses in Google Vids hint Nano Banana Pro is built for sharper visuals in creative tools. System shift:Google’s stacking its apps behind a single backbone: Gemini 3 Pro. .. read more
Hey, sign up or sign in to add a reaction to my post.
Hey there! 👋
I created FAUN.dev(), an effortless, straightforward way for busy developers to keep up with the technologies they love 🚀
