From Paging to Postmortem: Google Cloud SREs on Using Gemini CLI for Outage Response
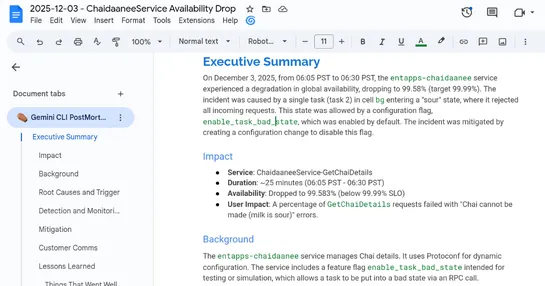
Google Cloud SREs just leveled up their incident response game with theGemini CLI- an LLM-fueled terminal sidekick built onGemini 3. It jumps in fast: drafts mitigation playbooks, digs into root causes, and cranks out postmortem reports. All withhuman-in-the-loopguardrails to keep things sane... read more